A while back I had a need to check all the servers in my domain and see what services were logged in with “special” accounts. In other words, find any service that’s not running off of a default builtin account. A script like this comes in very handy when it comes time to update the password on an AD account that might be used out there on a service but you aren’t 100% sure where its used in the environment anymore.
The usual disclaimer…yes I am sure there is another way to do this, especially if you are more well versed in PS but this does work and gives clean output so feel free to use it if you like.
 First thing I did with this one if suppress the errors, reason being is that when the script tests the machine for being on, if the machine is off/doesn’t exist anymore and it will throw an error for not being able to communicate with the machine. I didn’t do it in mine because I know the environment well as far as machines that are in use and machines that aren’t but down a little lower in our script you could always build in a simple, clean, user friendly response saying that the script was unable to contact the machine.
First thing I did with this one if suppress the errors, reason being is that when the script tests the machine for being on, if the machine is off/doesn’t exist anymore and it will throw an error for not being able to communicate with the machine. I didn’t do it in mine because I know the environment well as far as machines that are in use and machines that aren’t but down a little lower in our script you could always build in a simple, clean, user friendly response saying that the script was unable to contact the machine.
Next we have to figure out where we are going to get the info, where the list of machines is going to come from. If you wanted you could have a static list that gets updated and store it in a file or in a DB if that is your style. If you think though there is already a list we can get at, every time a machine is added to Active Directory, AD keeps an entry for it so its easy to use what is already there.

Take a look at that line of code, pretty simple. All it does is load the results from a simple AD query that looks for Computers in AD with the OS containing the word “server”. Once this query runs you will have a nice list of any servers listed in the AD.
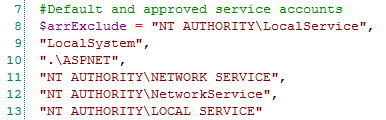
Once you have the list of servers we are going to want to define a list of things that you don’t want, which means anything that is running under “normal” service logins. The code below creates an array of the normal ones in my environment, this list can certainly be augmented just remember to use a comma between entries.
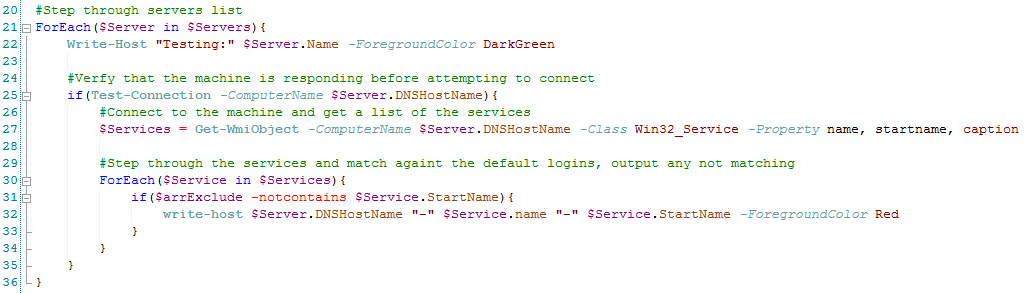
Now that all the leg work is done to get the supporting data the actual search can be done:
 So, the code above isn’t that bad. Line 21 simple starts a ForEach block to step through the servers in the list that we got earlier. I like to make things as easy and informative as possible so the next line just outputs to the screen, in Green, what machine name is being queried. Before I actually query the services on a machine I just want to check if its on so on line 25 is a simple IF statement, if the machine responds to a PING request then query the services, if not, then move on. The actual query of the services takes place on 27 using WMI against the class Win32_Service and stores the info to the variable for us to use in a second.
So, the code above isn’t that bad. Line 21 simple starts a ForEach block to step through the servers in the list that we got earlier. I like to make things as easy and informative as possible so the next line just outputs to the screen, in Green, what machine name is being queried. Before I actually query the services on a machine I just want to check if its on so on line 25 is a simple IF statement, if the machine responds to a PING request then query the services, if not, then move on. The actual query of the services takes place on 27 using WMI against the class Win32_Service and stores the info to the variable for us to use in a second.
If you aren’t familiar with WMI classes a handy download would be a WMI Explorer, there are a bunch out there so just take a look around and download one that looks easy for you to use if you think it might help you.
The very last portion is stepping through the variable that holds the service entries we just gathered, this starts on line 30. Here we step through one service at a time and simply check the “StartName” property with the -notcontains switch. So, that means that we using that list we created earlier of service logins that we aren’t worried about and seeing if one of them is in use or something else. If something else is in use then we output that to the screen nice and pretty in Red so that whoever is running this script can clearly make it out.